Enterprise productivity platforms are entering a new phase. Instead of simply automating predefined workflows, tools like Microsoft’s emerging Copilot Cowork concept promise something far more ambitious: AI agents capable of executing complex, multi-step tasks across platforms such as Microsoft 365.
These systems represent a shift from automation to delegation. Instead of defining every step of a process, employees describe an outcome and the agent determines how to achieve it—sending emails, updating documents, adjusting permissions, or coordinating across applications.
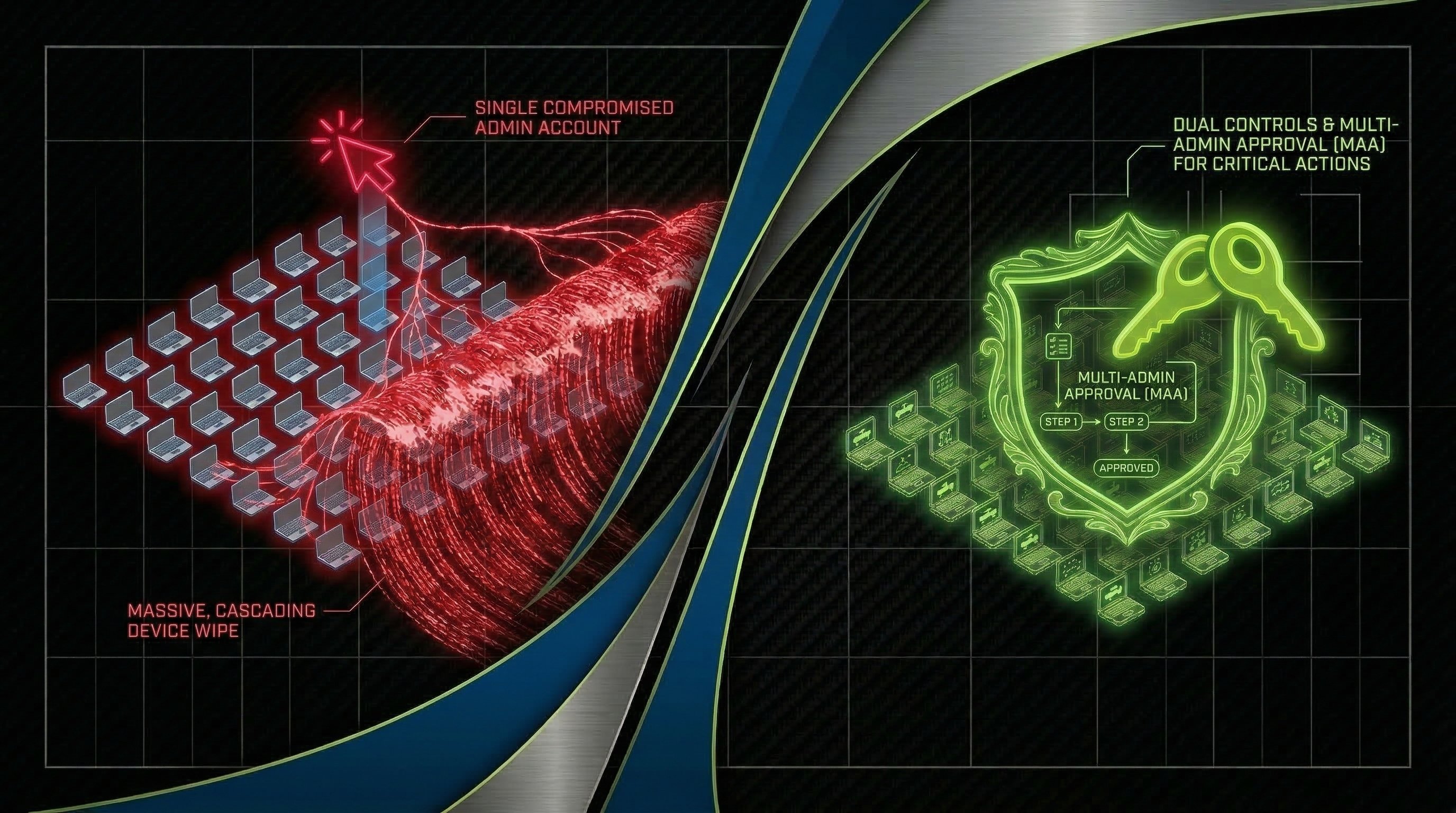
The Illusion of Oversight: Why Enterprises Need New Governance for Agentic AI in the Workplace
Lessons from Strkyer: Dual Controls, Multi-Admin Approval & Recent Cyberattacks
Written by Willie Zhang and Keegan Paisley
On March 11th, medical technology manufacturer Stryker disclosed a cybersecurity incident affecting its internal IT systems. The attack caused a global disruption to the company's Microsoft environment. Stryker activated its incident response process and brought in outside cybersecurity specialists.
Topics: Cybersecurity, Information Security, Incident Response, healthcare, Compliance, GRC
When Every Minute Counts: A Guide to Incident Recovery
A cybersecurity incident doesn't pause while your team figures out what to do next. Every minute an attacker remains in your environment, they have more time to expand their foothold, exfiltrate data, or encrypt additional systems — and the business is losing money the entire time. But here's the critical nuance most organizations miss: the goal isn't to start recovering as fast as possible. It's to understand what you're dealing with and contain the incident first.
Topics: Data Breach, Information Security, Incident Response, cybersecurity insurance, Cybersecurity Consulting
ClickFix: The Latest Twist in Social Engineering Scams
ProCircular has been monitoring a troubling uptick in ClickFix attacks—a sneaky form of social engineering that tricks users into running harmful scripts on their systems. This type of attack is particularly clever, masquerading as legitimate interactions to catch users off guard.
Topics: Cybersecurity, Data Protection, Security Awareness Training, MXDR, social engineering
StealthCraft: Unveiling the Path to Total Domain Domination
With EDR (Extended Detection and Response) becoming more necessary and common, it begs the question of what tactics and techniques are evading these protections. ProCircular recently conducted a penetration test involving evasion methods that did just that by successfully bypassing EDR protections by leveraging lay-of-the-land tools and incident response techniques. Our objective was to achieve full domain compromise within the targeted network, demonstrating the vulnerabilities and potential weaknesses that need to be addressed for robust cybersecurity. A walkthrough of the attack can be examined below.
Topics: Cybersecurity, Penetration Testing, Incident Response, hacking