What shadow AI really looks like inside a normal workday
Shadow AI is any AI tool, feature, or integration your organization uses without clear approval, security review, or monitoring, but it still touches real business data. It’s the AI sidebar in your CRM, the browser extension a manager added, or an “assist” feature turned on by a vendor.
Read More
Topics:
Cybersecurity,
HIPAA,
Information Security,
Compliance,
AI,
Artificial Intelligence,
AI Cyber
Written by Willie Zhang and Keegan Paisley
On March 11th, medical technology manufacturer Stryker disclosed a cybersecurity incident affecting its internal IT systems. The attack caused a global disruption to the company's Microsoft environment. Stryker activated its incident response process and brought in outside cybersecurity specialists.
Read More
Topics:
Cybersecurity,
Information Security,
Incident Response,
healthcare,
Compliance,
GRC
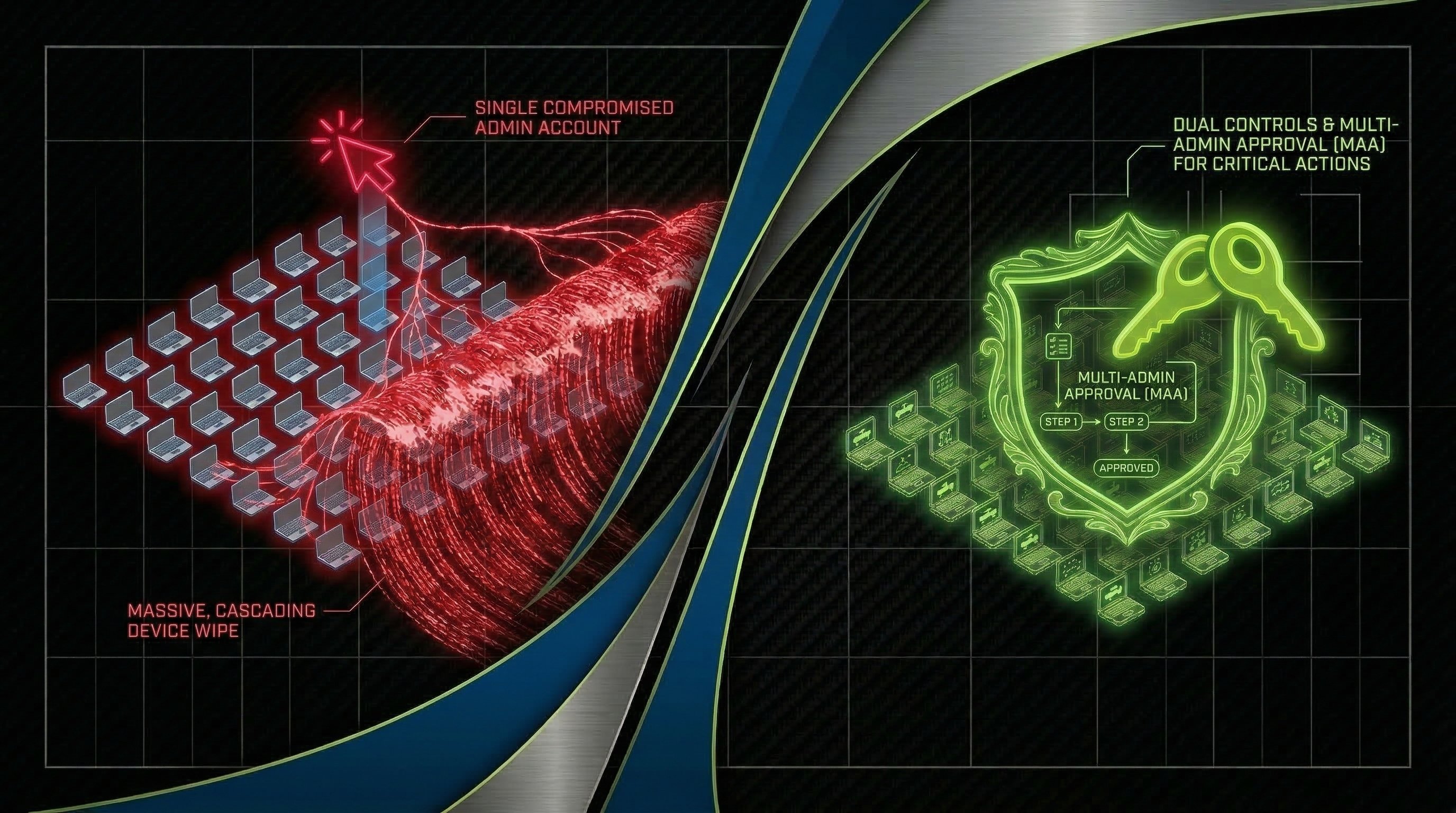
A cybersecurity incident doesn't pause while your team figures out what to do next. Every minute an attacker remains in your environment, they have more time to expand their foothold, exfiltrate data, or encrypt additional systems — and the business is losing money the entire time. But here's the critical nuance most organizations miss: the goal isn't to start recovering as fast as possible. It's to understand what you're dealing with and contain the incident first.
Read More
Topics:
Data Breach,
Information Security,
Incident Response,
cybersecurity insurance,
Cybersecurity Consulting
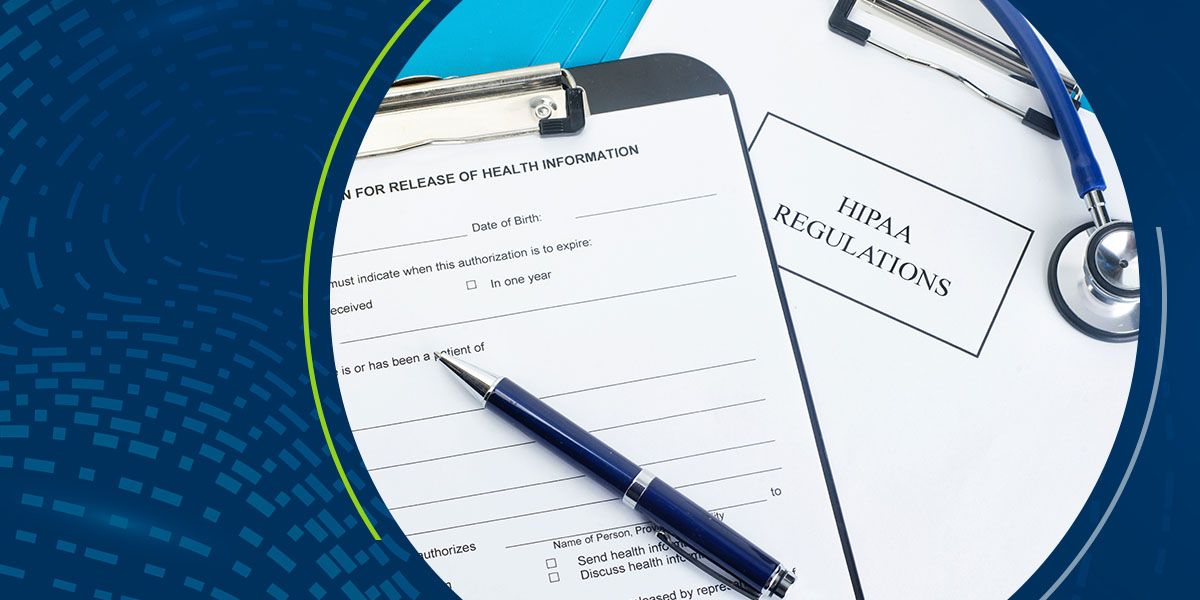
In January 2025, the U.S. Department of Health and Human Services (HHS) introduced proposed updates to the HIPAA Security Rule, aiming to close security gaps and strengthen protections for electronic protected health information (ePHI). These changes come in response to an alarming rise in cyberattacks in the healthcare sector, where ransomware and data breaches have affected millions of patients and cost the industry billions of dollars.
Read More
Topics:
Cybersecurity,
HIPAA,
Data Breach,
Information Security,
Data Security,
Data Protection,
healthcare,
Passwords,
Risk Assessment,
Ransomware,
MFA,
Compliance,
Policies & Procedures
It’s hard to believe that we survived 2024, and with 2025 finally here, we thought we would present where ProCircular sees the world headed. The cybersecurity landscape continues to evolve at a breakneck pace, driven by AI-enabled threats and an increasingly complex world. From deepfake videos to targeted social engineering, attackers are finding new ways to exploit trust and access critical systems.
Read More
Topics:
Cybersecurity,
Network Security,
Data Breach,
Information Security,
Data Security,
Data Protection,
Security Awareness Training,
healthcare,
hacking,
Manufacturing,
Passwords,
risk,
Ransomware,
Banking,
Financial Institutions