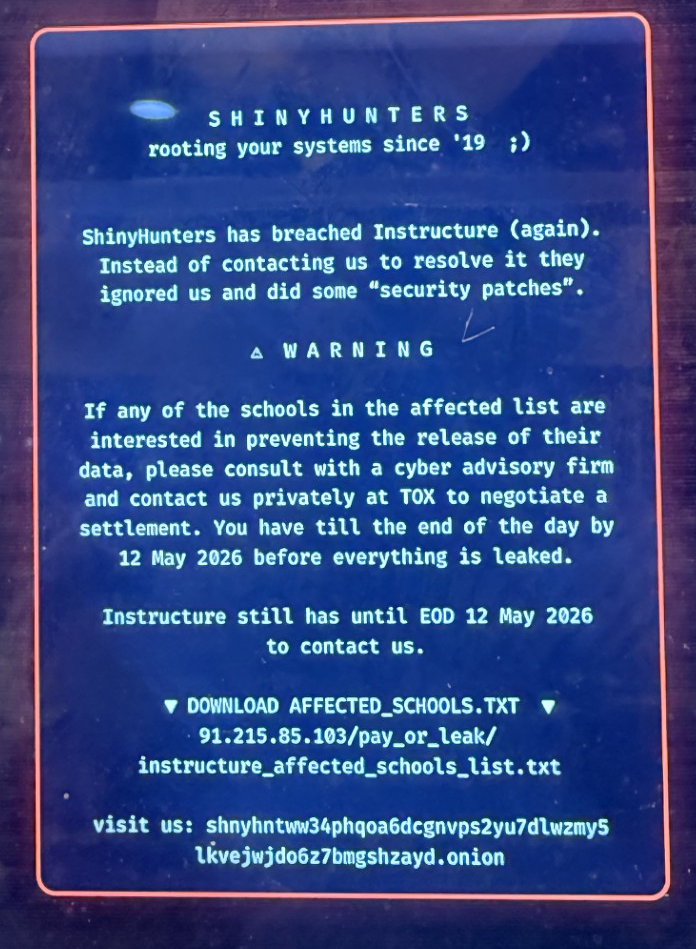
Many of you have seen the headlines about the breach at Instructure, the company behind the Canvas learning management system used by 41% of higher education institutions in North America and thousands of K-12 districts. Here's what's known, and what your institution should be doing about it.
Topics: Incident Response, Ransomware, Policies & Procedures, AI
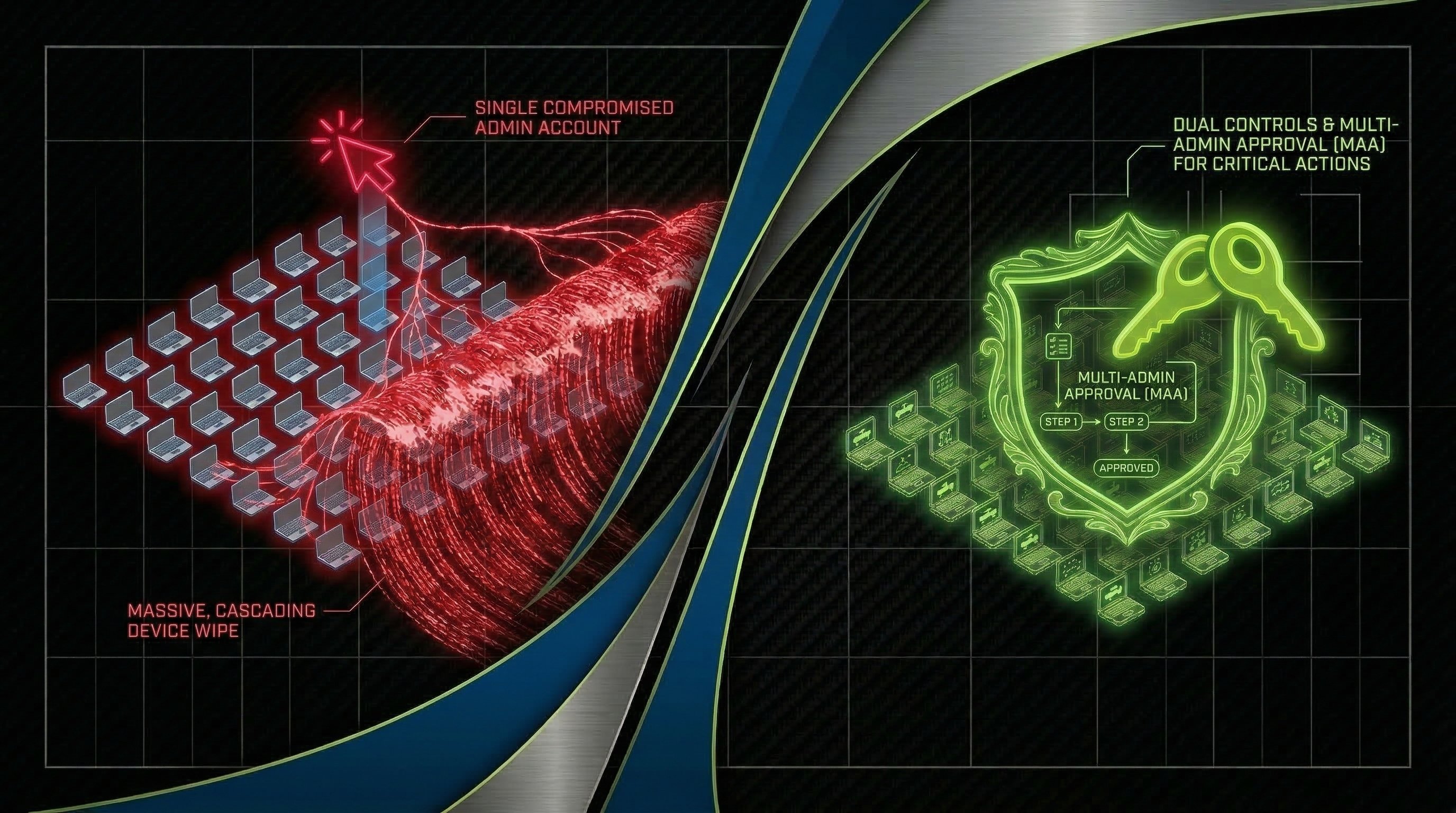
Lessons from Strkyer: Dual Controls, Multi-Admin Approval & Recent Cyberattacks
Written by Willie Zhang and Keegan Paisley
On March 11th, medical technology manufacturer Stryker disclosed a cybersecurity incident affecting its internal IT systems. The attack caused a global disruption to the company's Microsoft environment. Stryker activated its incident response process and brought in outside cybersecurity specialists.
Topics: Cybersecurity, Information Security, Incident Response, healthcare, Compliance, GRC
When Every Minute Counts: A Guide to Incident Recovery
A cybersecurity incident doesn't pause while your team figures out what to do next. Every minute an attacker remains in your environment, they have more time to expand their foothold, exfiltrate data, or encrypt additional systems — and the business is losing money the entire time. But here's the critical nuance most organizations miss: the goal isn't to start recovering as fast as possible. It's to understand what you're dealing with and contain the incident first.
Topics: Data Breach, Information Security, Incident Response, cybersecurity insurance, Cybersecurity Consulting
StealthCraft: Unveiling the Path to Total Domain Domination
With EDR (Extended Detection and Response) becoming more necessary and common, it begs the question of what tactics and techniques are evading these protections. ProCircular recently conducted a penetration test involving evasion methods that did just that by successfully bypassing EDR protections by leveraging lay-of-the-land tools and incident response techniques. Our objective was to achieve full domain compromise within the targeted network, demonstrating the vulnerabilities and potential weaknesses that need to be addressed for robust cybersecurity. A walkthrough of the attack can be examined below.
Topics: Cybersecurity, Penetration Testing, Incident Response, hacking
As businesses evolve to achieve higher security maturity, threat actors and penetration testers must also rise to the challenge. Modern third-party security applications such as Endpoint Detection and Response (EDR), Extended Detection and Response (XDR), Windows Defender products, and application allowlists have made offensive tools obsolete. Gone are the days when all a penetration tester needed was a remote shell or desktop connection to extract user data and credentials from local machines and domain controllers. Instead of fighting against signature-based and obfuscation methods, attackers are turning to digital forensics incident response (DFIR) tools, like KAPE, to get the dirty work done for them. After all, you never have to sneak into the party if the bouncer thinks you’re already on the list.
Topics: Cybersecurity, Incident Response, hacking