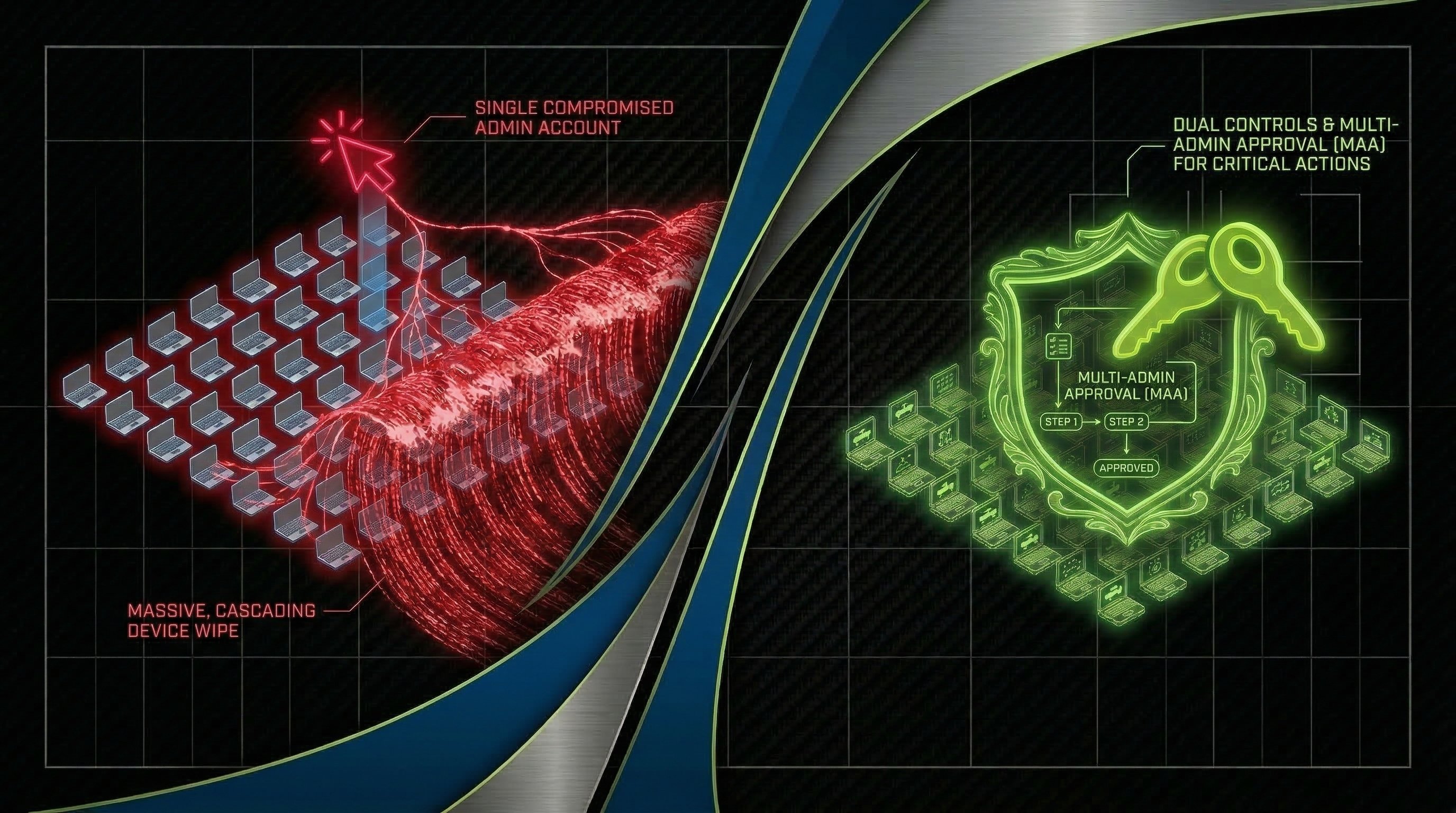
What shadow AI really looks like inside a normal workday
Shadow AI is any AI tool, feature, or integration your organization uses without clear approval, security review, or monitoring, but it still touches real business data. It’s the AI sidebar in your CRM, the browser extension a manager added, or an “assist” feature turned on by a vendor.