Security Information & Event Management, or SIEM (pronounced "sim," with a silent "e"), is gaining a reputation outside of the cybersecurity community. Advertisements on YouTube and Hulu tout the product’s incomparable security and real-time effectiveness, but they struggle to convey what a SIEM really does. Technical security lingo tends to make non-technical people tune out, and trying to simplify the concept diminishes its value.
Topics: Cybersecurity, Information Security, Data Security, SIEM
Three Cybersecurity Risks You Don’t Really Need to Worry About
As a non-technical person working in the cybersecurity industry, I often find myself asking, “Do I need to be worried about [insert novel threat]?” I am almost always pleased to learn that the experts have considered these threats and created simple protective measures so that no, I do not necessarily need to be worried about [insert novel threat]. In taking a few simple precautions, you might never need to worry about these intimidating cyber risks ever again!
Topics: Cybersecurity, Personal Privacy
A guide to creating challenging, educational, and enjoyable vulnerable virtual machines.
Picture this, you've just completed another machine on TryHackMe, Vulnhub, or HackTheBox and you're left thinking to yourself "well I'd quite like to build one of those for myself" but then you realize that you don't have any idea of where to start. Fear no more! In the following post, we'll break down the core ideas behind creating an excellent box.
Topics: Cybersecurity
Risk Rolling: Don’t Let Your Business Roll the Dice with Risk
New to the world of cybersecurity and wondering where to even begin? Ever wonder what it takes to become a professional hacker? Varying levels of IT knowledge and understanding? Everybody must start somewhere, and here is your chance! Reimagine your career as an Information Security Specialist and stop wasting your time with "what ifs." Allow yourself to grow and shine in a field that you are passionate about. Outreach your potential with this fantastic new course!
Topics: Cybersecurity, Information Security, risk
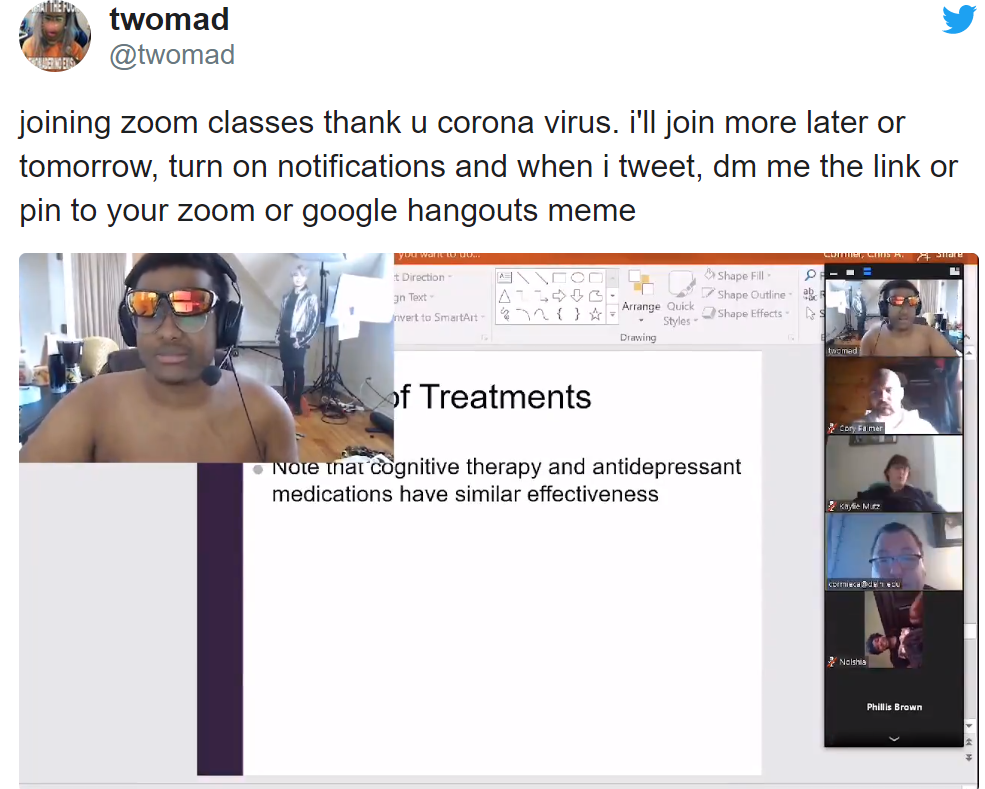
#Zoombombing, Nazi's, Kids, and Cybersecurity 2020
Zoom has been a big name in the headlines lately, mainly due to the world’s newfound dependence on, and perhaps obsession with, the platform. As global business is forced to move online, Zoom has become one of the most commonly chosen video conferencing platforms. It’s easy to use, simple to roll out, and the company has provided free and low-cost licenses to both public and private organizations.
Topics: Cybersecurity, consumer security, hacking


-1.jpeg)