Zoom has been a big name in the headlines lately, mainly due to the world’s newfound dependence on, and perhaps obsession with, the platform. As global business is forced to move online, Zoom has become one of the most commonly chosen video conferencing platforms. It’s easy to use, simple to roll out, and the company has provided free and low-cost licenses to both public and private organizations.
Like any technology or software platform, Zoom has risks. This rapid increase in demand has highlighted some of the platform’s inherent weaknesses. These types of failures would be much less impactful and publicized in a time of slower adoption of their solution.
As a result, the news has been filled with the new verb “Zoombombing,” and the examples have tended to amplify themselves. In this blog, we will take a deep dive into the hype, provide real examples of these weaknesses and their impact, and offer fixes that will better secure your use of any online video conferencing tool.
So... what is Zoombombing?
“Zoombombing” has only existed for a couple of weeks at the time of writing this article, but the idea isn’t new. An individual or group will discover an open meeting and “crash” the meeting without an invite. Typically, a group of people will gather, start their session, and be unexpectedly joined by an unruly group of uninvited guests looking to cause trouble. This is not a novel concept, whether in the form of party crashers or prank phone calls. A Bart Simpsonesque call to Moe’s Tavern asking for “Al Coholic” or “I.P. Freely” really isn’t much different from the vast majority of these malicious Zoom crashes.
Unfortunately, though, there is a darker side to this version of the prank call. As many schools have adopted Zoom as a make-shift educational platform, these “Zoombombings” can be seen as someone pulling a fire alarm during school hours. In the worse case, they’re antisemitic, racist, and hurtful. Some are vindictive enough to have raised the ire of the FBI. The bureau recently stated, “We are distraught to hear about the incidents involving this type of attack, and we strongly condemn such behavior.”
Recent Attacks
The range of recent attacks spans from childish pranks to horrible bunk. A few examples are listed below:
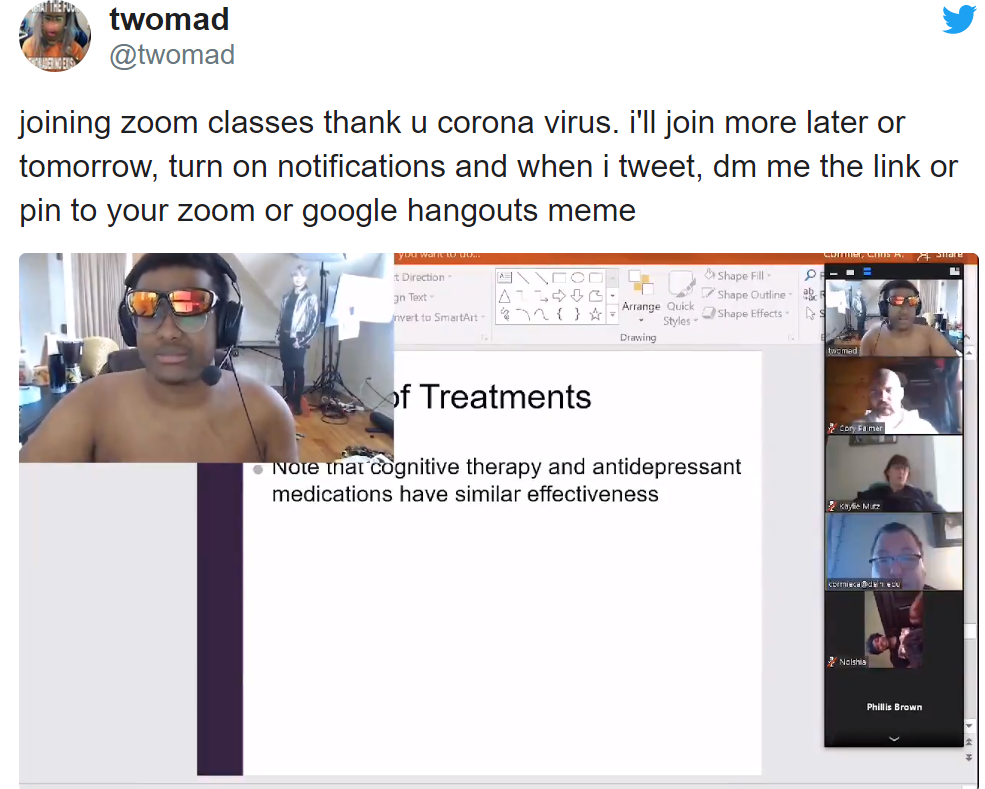
An example of a Zoombomber jumping into the middle of a class being held online.

The above is a meeting of a group of New Yorkers where a Zoombomber posted 9-11 memes and images.

Several Jewish organizations have been targeted with anti-Semitic hate speech.
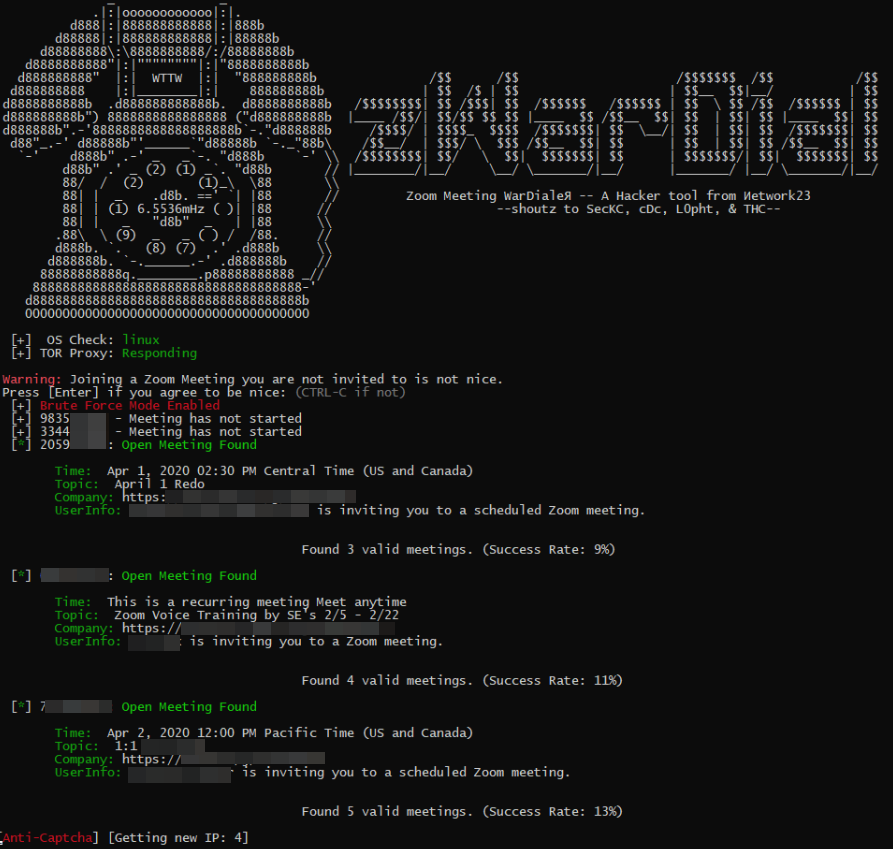
Reddit is awash with complaints and comments (more on that later)
Many more examples can be found here or by searching Twitter for the #zoombombing
How it Happens
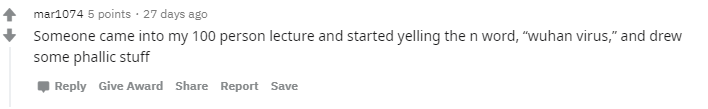
A member of a research group called SecKC developed a tool called zWarDial, something akin to the time-tested modem scanning that would simply search through phone numbers (319)-354-0001 thru (319)-354-9999 looking for a target. It avoids some of Zoom’s built-in tools by scanning from a variety of countries and I.P. addresses and claims to be able to find somewhere around 100 meetings per hour. In the wrong hands, this tool can open organizations with disabled passwords relatively quickly.
https://krebsonsecurity.com/2020/04/war-dialing-tool-exposes-zooms-password-problems/comment-page-1/
Kids Invites
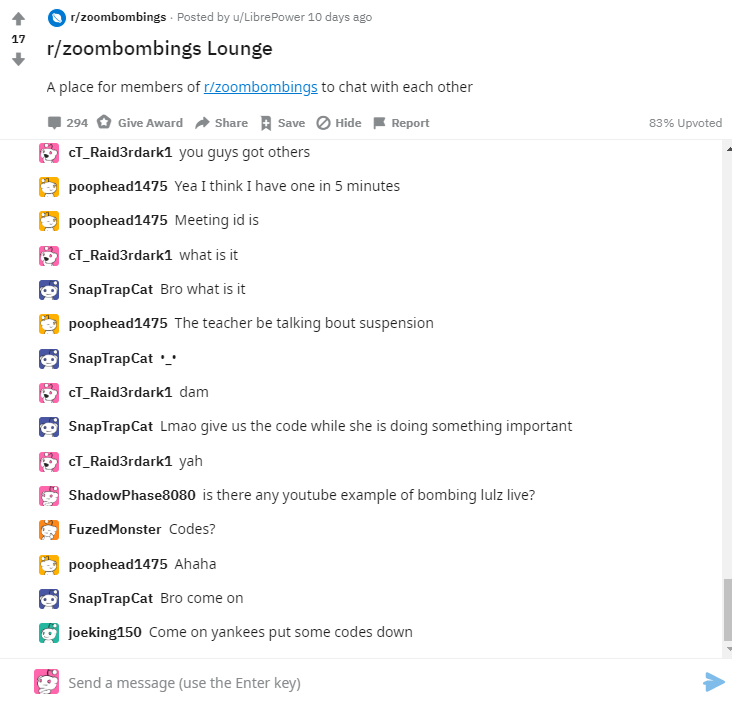
As is usually the case, the simplest explanation is the most common. The tech-savvy generation of kids who are stuck learning online are quick to look for entertainment and a distraction. The following image is a screen capture from 4-22-2020 at 2:30 pm in a live Reddit lounge. Kids are sharing invites and meeting pins with larger groups of would-be Zoombombers to invite them to break up the class and bring some happiness to an otherwise dangerous situation.
Darker Side
Recently, a vulnerability was uncovered that allows a more sophisticated hacker to insert an executable and force it to execute through the chat feature of the platform. Zoom has moved quickly to remedy the situation. It has (as of right now) patched this specific vulnerability, but it’s likely that other weaknesses will be discovered as the platform matures.
An example of this vulnerability in practice is available here: https://www.youtube.com/watch?v=Om1w4DVkkEU
Zoom, Inc.
To their credit, Zoom, Inc. has done a fantastic job of handling not only the inherent risks of their platform, but the massive increase in volume with the need to work from home during the pandemic. Zoom’s founder and CEO, Eric Yuan, wrote in an April 1st blog post that “the maximum number of daily meeting participants, both free and paid, conducted on Zoom was approximately 10 million,” as of the end of December last year. This figure soared to “more than 200 million daily meeting participants” in March.
They’ve also made strenuous efforts to respond to the various issues that have emerged as demand has gone through the roof. The company has rolled out higher levels of encryption, stepped up their support for HIPAA and FERPA compliance to support healthcare and education, and rolled out constant updates to patch issues as they’re identified. They’ve also been rather transparent with their security issues. On April 15 alone they announced:
- Changes to Zoom’s default settings
- Enhanced password security
- Changes to data center routing
- A bug bounty program
- A new security icon to provide better security features to hosts.

Zoom’s stock has skyrocketed as a result of this increased demand for their services. Long term, it’s likely that organizations (like ours) which have historically resisted a work-from-home approach will become more comfortable with this platform, resulting in higher long-term value in Zoom’s organization.
Avoiding Problems
As with any software program, there are some simple steps that one can take to prevent 90% of the issues that seem to plague others. Following these five suggestions may be the difference between the usual problems (who’s muted, why doesn’t this camera work, who doesn’t get that we can see them), and more severe issues with hackers.
- Create a unique Meeting ID - There’s a good chance that others can find your ‘personal’ Zoom meeting I.D. If you’ve done a webinar in public, the chances are that it’s out in the wild and can be located. You should always generate a random meeting I.D. for each meeting.
- Always use a meeting password - Create new passwords each time, and share them only with required attendees. This approach may not work in education fields where pesky kids may share them anyway, but a unique password each time cuts down on the likelihood of interruption.
- Waiting rooms are your friend - Just as bars have bouncers, it’s a good idea for any meeting to have a moderator who decides whether or not the people attempting to join should be allowed into the club.
- Mute by default - While not always an option for smaller meetings, if you have more than ten people on a call, this should be a requirement to reduce the likelihood of that Zoombomber trying out a new swear word during your presentation.
- Disable screen sharing for everyone but host/panelists - A picture is worth a thousand words, and the wrong shared image or video may catch your attendees by surprise. By disabling this option for attendees, you can eliminate the chance that someone can shock your attendees.
In Closing
Zoom is a great platform, and the gallery feature alone puts it head and shoulders above many of the other services available. We hope that you enjoy both your company’s virtual strategy discussion as well as your Zoom Social Fridays in a safe, secure, and private way.
As always, if you need any assistance or have a severe risk to your organization as a result of your use of Zoom, please don’t hesitate to reach out to ProCircular.


