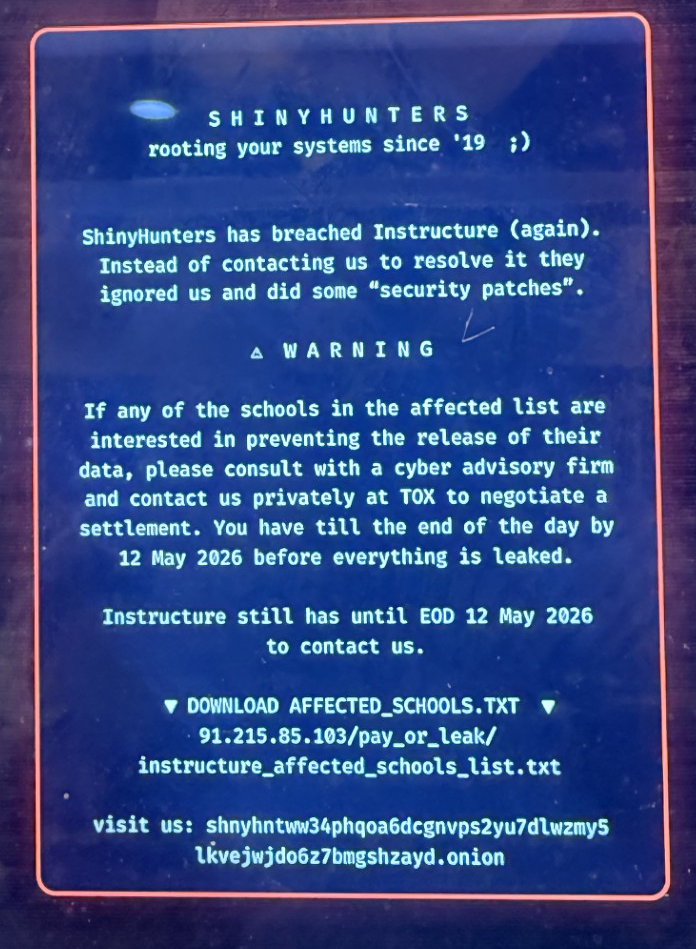
Many of you have seen the headlines about the breach at Instructure, the company behind the Canvas learning management system used by 41% of higher education institutions in North America and thousands of K-12 districts. Here's what's known, and what your institution should be doing about it.
Topics: Incident Response, Ransomware, Policies & Procedures, AI
How the New HIPAA Security Rule Changes Will Affect Healthcare
In January 2025, the U.S. Department of Health and Human Services (HHS) introduced proposed updates to the HIPAA Security Rule, aiming to close security gaps and strengthen protections for electronic protected health information (ePHI). These changes come in response to an alarming rise in cyberattacks in the healthcare sector, where ransomware and data breaches have affected millions of patients and cost the industry billions of dollars.
Topics: Cybersecurity, HIPAA, Data Breach, Information Security, Data Security, Data Protection, healthcare, Passwords, Risk Assessment, Ransomware, MFA, Compliance, Policies & Procedures
It’s hard to believe that we survived 2024, and with 2025 finally here, we thought we would present where ProCircular sees the world headed. The cybersecurity landscape continues to evolve at a breakneck pace, driven by AI-enabled threats and an increasingly complex world. From deepfake videos to targeted social engineering, attackers are finding new ways to exploit trust and access critical systems.
Topics: Cybersecurity, Network Security, Data Breach, Information Security, Data Security, Data Protection, Security Awareness Training, healthcare, hacking, Manufacturing, Passwords, risk, Ransomware, Banking, Financial Institutions
Staying Vigilant Against Cyber Threats in Healthcare
Recently, the American Hospital Association warned that Black Basta, a known ransomware group, would be accelerating attacks within the healthcare sector. The group gained notoriety for their sophisticated attack methods and high-profile targets, and typically operates by infiltrating a network, exfiltrating sensitive data, and then encrypting the victim's files.
Healthcare organizations can stay vigilant against threat actors by adopting a comprehensive cybersecurity strategy that incorporates regular testing and 24/7 monitoring. ProCircular also recommends the following:
Topics: Cybersecurity, Network Security, Data Breach, Information Security, Data Security, Data Protection, Security Awareness Training, healthcare, hacking, Passwords, risk, Ransomware
Cybersecurity Challenges for Trucking in 2024: Mitigating Risks on the Road
Buckle up, truckers! Trucking is the industry that keeps America rolling, and it's in the middle of a digital revolution. From high-tech ELDs to AI-powered cameras and internet-connected trailers, the way we haul goods is evolving at breakneck speed. In the interest of safety (and profit) most trucks now have or will soon get AI cameras for things like distracted driver, cell phone detection, gyro events, etc. But alongside these advancements lurks a hidden adversary – hackers.
Topics: Cybersecurity, Incident Response, Security Awareness Training, Ransomware, Transportation, Trucking, MFA