While essential functions of community colleges remain constant, the ever-changing digital landscape presents unique cybersecurity challenges. From talent retention to securing a diversifying data landscape, colleges must adapt their strategies to keep pace.
Community Colleges Navigate Evolving Cybersecurity Landscape in 2024
Topics: Cybersecurity, Data Breach, Data Security, vulerability assessment, hacking, community colleges
Sophisticated Threat Actors are using LinkedIn to Phish Employees
Phishing via employment-focused social media is on the rise. While performing incident response over the last few months, ProCircular encountered multiple incidents where LinkedIn was used in employee phishing attacks. Several news articles raised awareness of this phishing vector over the last year, and the trend continues with a new wave of attacks by sophisticated threat actors.
Topics: Incident Rsponse, hacking, risk
As a cybersecurity engineer and an unapologetically enthusiastic “web guy,” I have both a personal and professional interest in finding new exploitation methods. Recently, I found an interesting and creative way to control a browser by exploiting a cross-site scripting (XSS) vulnerability. I learn by doing, so I executed the concept to see it work in practice. Without spoiling too much, I was very pleased with the results! This attack uses nothing more than Netcat and some clever XSS injection code. For those unfamiliar with Netcat, it’s a networking utility that reads and writes data across network connections.
Topics: Network Security, Data Protection, Penetration Testing, hacking
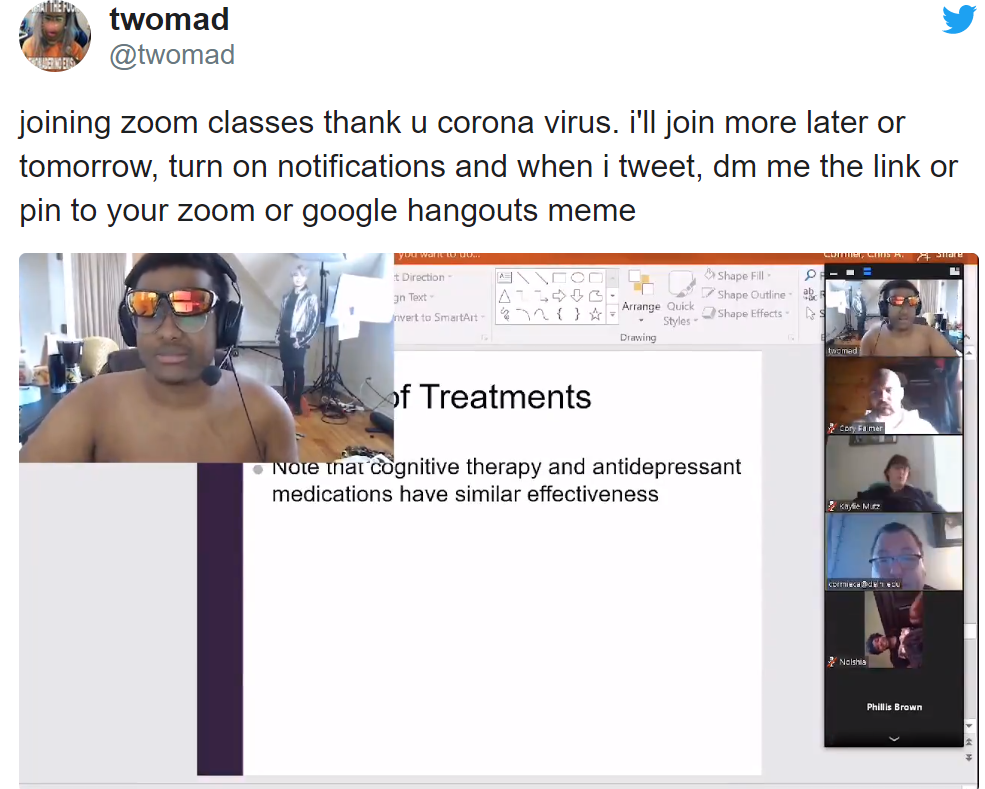
#Zoombombing, Nazi's, Kids, and Cybersecurity 2020
Zoom has been a big name in the headlines lately, mainly due to the world’s newfound dependence on, and perhaps obsession with, the platform. As global business is forced to move online, Zoom has become one of the most commonly chosen video conferencing platforms. It’s easy to use, simple to roll out, and the company has provided free and low-cost licenses to both public and private organizations.
Topics: Cybersecurity, consumer security, hacking
Imagine for a moment your favorite spy movie, maybe a James Bond movie for example. It’s cast of characters likely consists of five or so core archetypical personas. In this cast you likely have a cunning spy, a love interest, the shrouded head of the spy agency, the maniacal bad guy, and a clever hacker sitting in the background. Swooping in seemingly at a moment’s notice to disarm a security system or provide intel about a target’s movements, the hacker always seems to be a mysterious figure with deus ex machina powers. In the following article, we’ll dive into this archetypical figure, breaking down the driving factors behind hacking and the overall ideas behind what makes a hacker ‘tick’.
Topics: Cybersecurity, hacking