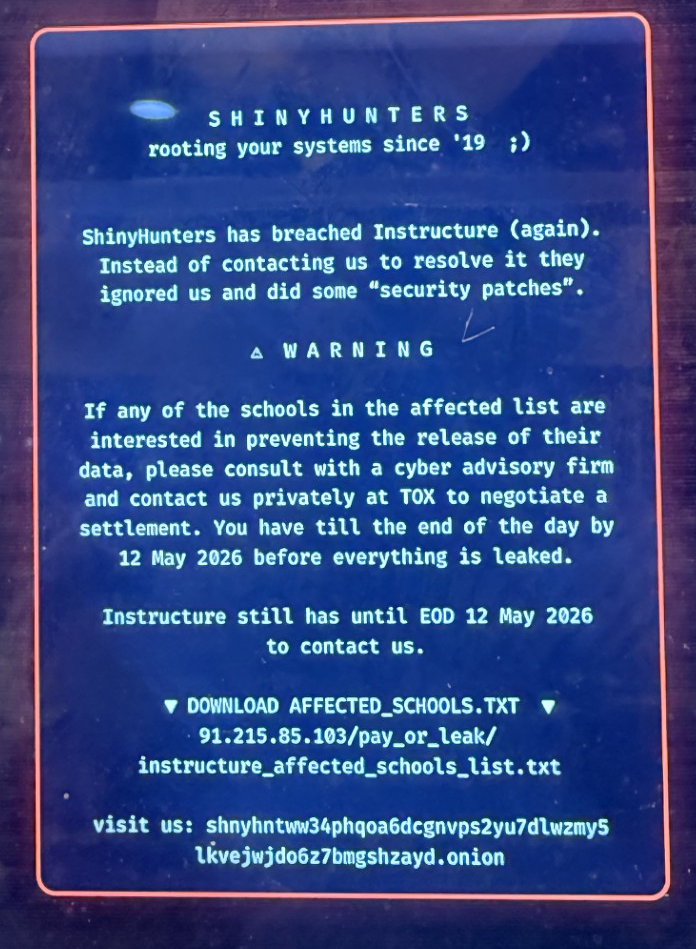
Many of you have seen the headlines about the breach at Instructure, the company behind the Canvas learning management system used by 41% of higher education institutions in North America and thousands of K-12 districts. Here's what's known, and what your institution should be doing about it.
Topics: Incident Response, Ransomware, Policies & Procedures, AI
Shadow AI: The Risk Your Security Tools Can’t See
What shadow AI really looks like inside a normal workday
Shadow AI is any AI tool, feature, or integration your organization uses without clear approval, security review, or monitoring, but it still touches real business data. It’s the AI sidebar in your CRM, the browser extension a manager added, or an “assist” feature turned on by a vendor.
Topics: Cybersecurity, HIPAA, Information Security, Compliance, AI, Artificial Intelligence, AI Cyber
Mythos & Glasswing are complicated and new. Jim is going to help us understand...
Two weeks ago, Anthropic announced that its newest AI model was too dangerous to release to the public. The Claude Mythos Preview reportedly found critical software vulnerabilities, including some that had gone undetected for over twenty years. In response, Anthropic launched Project Glasswing, a $100 million coalition that includes Apple, Microsoft, Google, AWS, JPMorgan Chase, CrowdStrike, the Linux Foundation, and about fifty other major industry players. Their goal is to find and fix the most serious issues before attackers do. That was the main story.
Topics: AI, Artificial Intelligence, Claude, Mythois, Offensive Security, AI Cyber
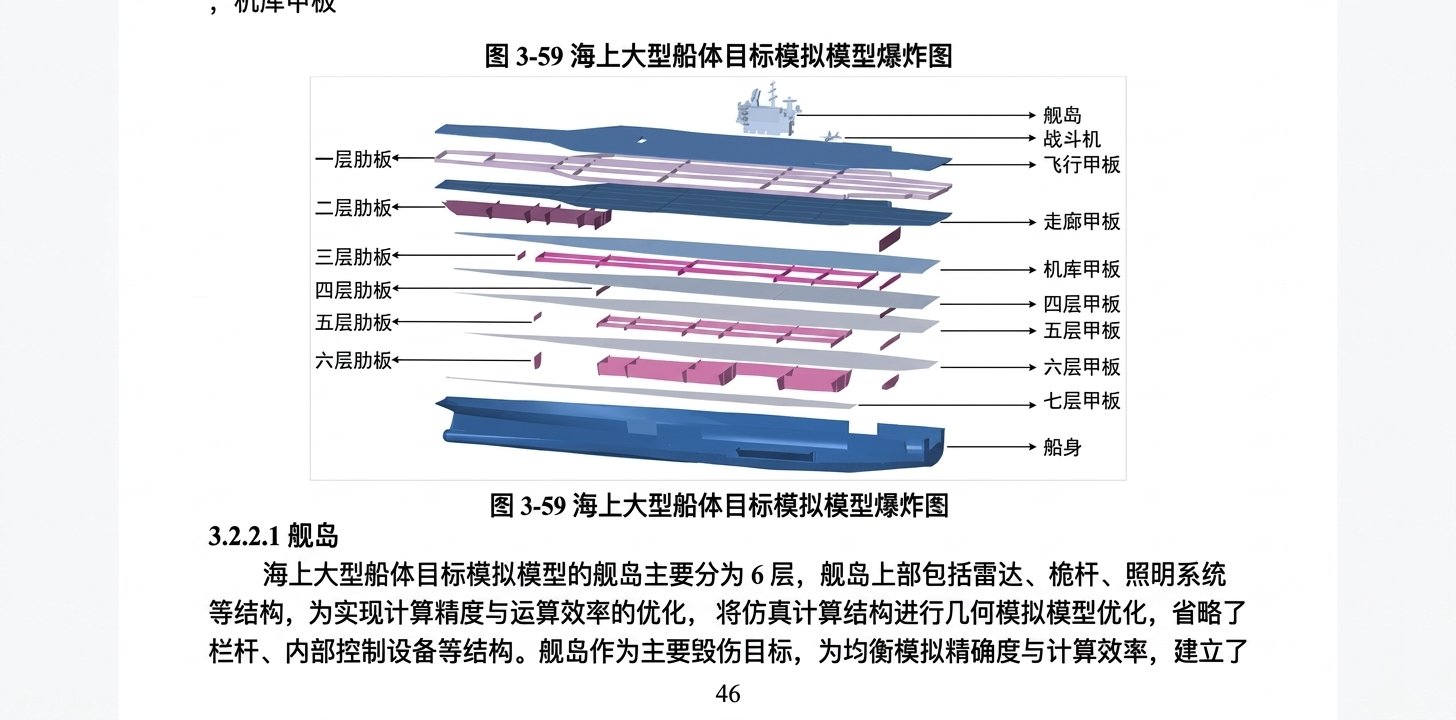
The 10-Petabyte Heist: The Recent China Supercomputing Breach Means
If you've been in cybersecurity long enough, you develop a reflex: dramatic claims usually aren't true. So when a tweet started circulating in early April 2026 alleging 10 petabytes of data had been stolen from China's National Supercomputing Center in Tianjin—including defense documents and missile research—my reaction was the same as most practitioners: prove it. This brings us to the crucial question: did it really happen?
Topics: Cybersecurity, Penetration Testing, Monitoring, MXDR, Policies & Procedures, china
I spoke with a reporter this morning who asked me a simple question: Why do kids turn to cybercrime? After some fun and genuinely insightful conversations with my colleagues at ProCircular, ages 20 to 55+, here’s what we were able to cobble together.
Topics: Cybersecurity, Cybersecurity Consulting