There’s something powerful about bringing a roomful of Iowa technology professionals together to talk about forward-thinking ideas. You quickly realize how cybersecurity and data breaches truly impact every organization and everyone – and that no organization is ever too small to have a plan.
Cybersecurity: What All Companies Need to Think About
Topics: Cybersecurity, Data Breach, Iowa Tech Summit, Quantum Computing, Digital Rights Management
Information Security Costs: Budgeting for Cybersecurity
Budget season is upon us. Are you using this time to establish or improve your cybersecurity strategy?
Topics: Cybersecurity, budgeting
Iowa’s Linn County Partners with ProCircular to Secure Elections
Cedar Rapids, IA, September 1, 2017 – Linn Count y Auditor & Commissioner of Elections Joel Miller has retained Iowa-based cybersecurity firm ProCircular to review Linn County’s voter registration and election system. The effort will support the upcoming county-wide school elections to be held on Sept. 12, 2017, in Linn County , Iowa.
Topics: Cybersecurity, government, municipality, hacking, election, voting
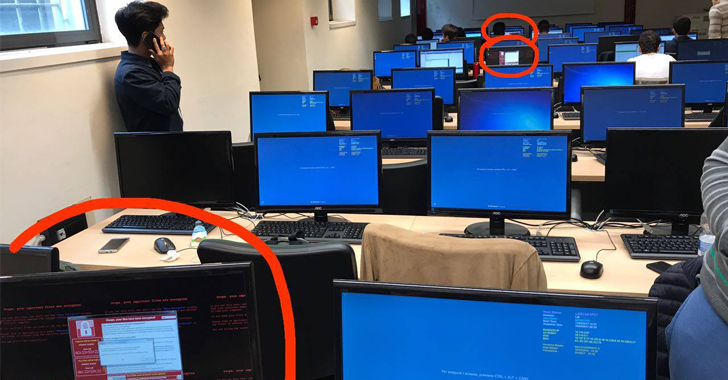
WannaCry: Solutions to the Latest Ransomware Challenge
Topics: Cybersecurity, Data Breach, Incident Rsponse, Incident Response, it risk assessment, healthcare
Industry Trends
Cybersecurity in the healthcare field has gone through a lot changes the past few years. In 2016 there was a significant jump in the total number of healthcare specific cybercrimes. According to SecurityIntelligence there was a 71% increase of confirmed data breaches in the healthcare sector from 2015 to 2016. Drilling down on that increase revealed that most of the jump was from external (aka "hacking" or ransomware or malware") followed by internal non-malicious (aka accidents from insiders). Trends are showing that cybercriminals have found more value in healthcare data and the potential for long term use is much higher because it is more difficult to change an individual’s "health data". Another eye-opener is that the type of healthcare entities affected is not limited to hospitals. Business associates, specialized care providers and healthcare plan have all been targets for cyber crime. Oncology, anesthesiology, orthopedic, and radiology are a few of the specific entities that were in the top 10 largest healthcare breaches of 2016. This data tells us that cybercriminals will target or find data outside of the large medical providers and may even be targeting the organizations that have lagged behind in implementing security controls.
Topics: Cybersecurity, Network Security, HIPAA, Information Security, Data Security, healthcare