Phishing Attacks
During a phishing attack, attackers use social engineering and malicious emails to steal valid credentials from users. Attackers can use these credentials to begin more complicated attacks, or they can bundle and sell them to other cybercriminals. The attackers lie about their identity and objectives to collect login information from unassuming victims or to get them to download malicious content. These emails might ask you to enter your password into a spoofed login page or send that information directly back to the sender. Although these scams are well-known, they are occasionally hard to spot, and they have a high rate of success. If you don’t encounter many of these emails, they may be caught in your junk folder. If this is the case, your email filtering is working effectively and removing potentially harmful phishing attempts. There is no reason to recover phishing emails from a junk folder.
Extortion Attacks
Extortion emails work a little differently. In this increasingly popular type of attack, the hackers claim to already have access to some sensitive information. That information could include anything from login credentials to embarrassing photos. Whatever they choose is something designed to prompt an urgent and desperate reaction from the recipient. In the email, they lay out what they have against their target, then threaten to blackmail them for money.
These types of emails are designed to be scary. They are supposed to make the victim feel so frantic that they act without thinking. If you ever receive a threatening extortion email, remain calm and report it through the proper channels. In this post, we’ll break down a poorly written extortion email that was sent to my junk folder.
So how does this type of campaign work?
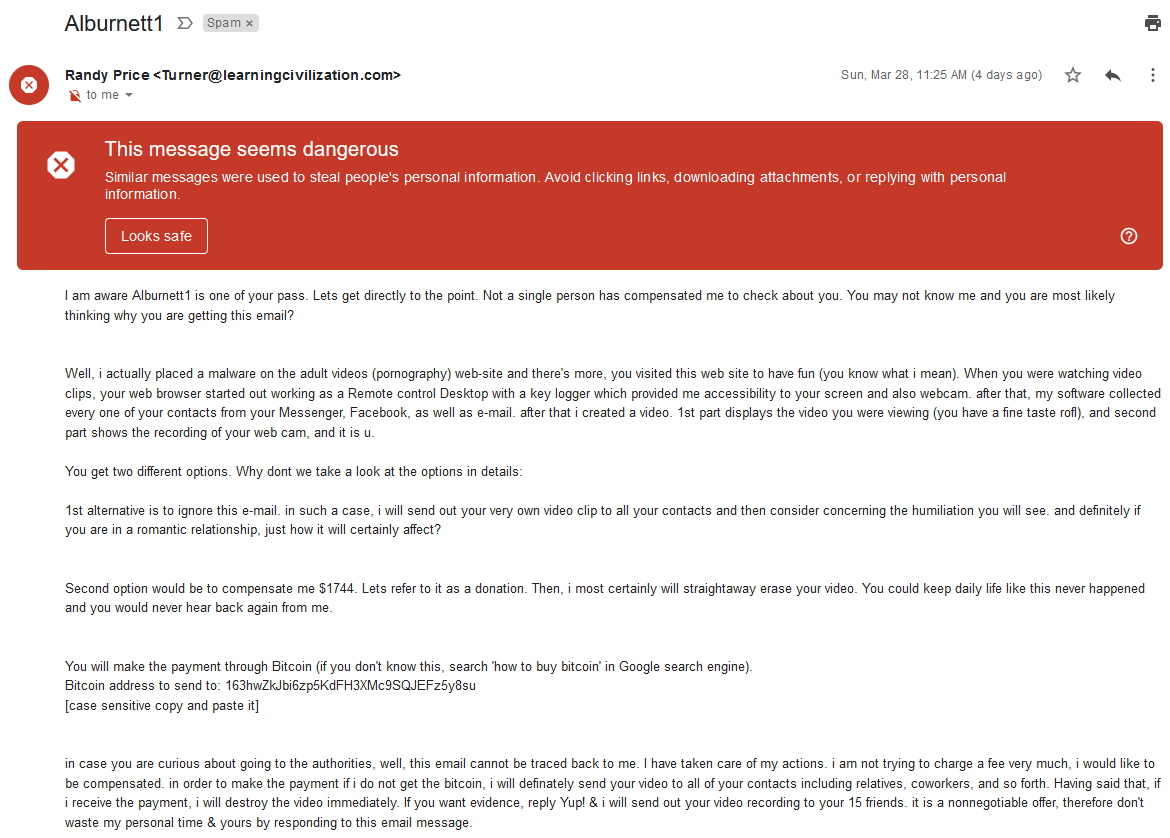
As you can see in the subject line and the first line of text, they mention a password that had been publicly breached and associated with one of my email addresses (yes, in middle school, before I got into cybersecurity, my go-to password was Alburnett1). There is not much you can do to avoid large-scale public breaches, but using MFA and limiting password reuse can help ensure your accounts are protected. In this attack, the threat actor finds all passwords associated with a publicly breached email address, then auto-populates the subject line and first line of the body, then send. Although Gmail sent the message straight to spam, different mail services may have different filtering rules.
Identifying Scams
These scam emails are created by social engineers to be tricky and manipulative. It’s not always easy to know which emails are malicious, but you can look for a few telltale indicators that you might be dealing with a scammer.
Firstly, do not fight the filter. There are very limited circumstances in which you should take messages out of your spam or junk folder and move them into your regular inbox. Generally, messages in the junk folder have been designated as harmful based on preconfigured settings. It’s far from foolproof, but it adds a layer of protection when successful social engineering tactics break down our typical defenses. In the example above, we see that the email has been flagged as potentially dangerous. Pay attention to these warnings, and proceed with caution, always assuming the sender is trying to deceive you.
As you begin analyzing the email, pay attention to the sender. Do you recognize the alias? Does the alias match up with the actual email address? Is their domain misspelled or otherwise fishy? In the example above, we see that the sender’s alias is listed as “Randy Price,” which does not align with the email address, Turner@learningcivilization.com. This indicates that the sender is trying to mislead victims for one reason or another. In these types of situations, it’s better to be safe than sorry. Avoid interacting with emails that you don’t recognize.
These campaigns work in mass. Although the correspondence may seem personally applicable to you, they’re running these scams against thousands of other user accounts. You can use this feature to your advantage by running the content of the email through an internet search. Copying and pasting the exact text into your search bar should return stories from other users who have been targeted. If another user has received and reported this email as a scam, you should consider following suit.
Other Avenues
These scams are not limited to email. Attackers also target users via phone calls known as “vishing” or “voice phishing” attacks. Highly technical actors can spoof a reputable caller ID to give their victims a false sense of security with the caller.
If you are ever contacted by someone requesting sensitive or personally identifiable information (PII), like your social security number, perform a little validating research before giving them anything. If the caller claims to be part of a reputable organization, politely end the call and find a validated phone number for that company, maybe from their website. Then, call that number directly. If the caller is a good guy, they should have no problem allowing you to perform this validation check. Again, it is better to be safe than sorry when it comes to protecting the privacy of your personal information. Remember, once the bad guys have your data, there is no way to get it away from them, so act with caution. Call screening technology is more accessible and possibly more necessary than ever. “Google Call Screen” is free software that adds a layer of validation between the caller and the recipient.
Key Takeaways
Email and telephone attacks use social engineering to manipulate users. Unassuming users are made to feel shameful, helpless, and frantic. Resisting these automatic reactions could help you respond more appropriately. The best way to protect yourself is to remain calm and vigilant any time you correspond with someone you don’t know. Pay attention for telltale factors like suspicious sender addresses, threatening tones, and auto-generated warnings.
These predators seek out well-meaning individuals who lack internet literacy or are otherwise vulnerable. If you ever feel like a stranger is asking too much of you, proceed with caution, maybe consult a friend. Perpetrators that ask you to keep their actions secret should not be trusted. If they request your secrecy, excessive urgency, or blind compliance, end the conversation immediately and report the offender through the proper channels. Safe and reputable organizations are aware of these schemes, and they should have no issue with your verification checks, like searching for the verified phone number online or researching the scenario they have presented to you. Never feel guilty for asking questions or ending a conversation with a stranger that makes you uncomfortable.
The victims of these vicious attacks shouldn't feel like they are at fault, but informing or creating boundaries for vulnerable people could help prevent major loss. If you’d like to discuss social engineering testing and preparedness, click here or call 844-95-SECUR to connect with one of ProCircular’s experts!