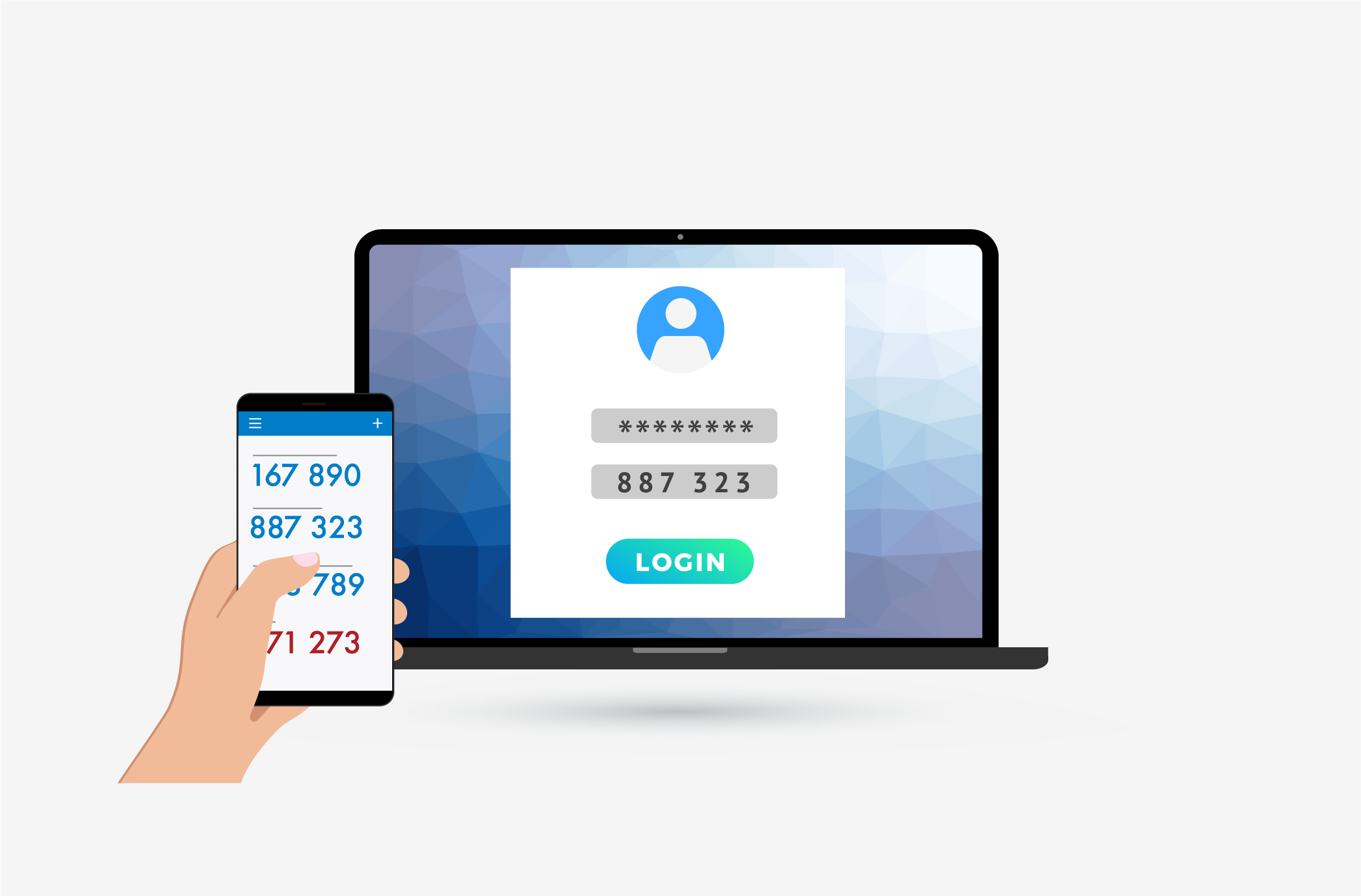
At this point, everyone has probably heard a speech about how important it is to have a strong password. It is true that a strong password is extremely important in preventing an attacker from guessing or cracking it. However, it does not help against those annoying and ever-present phishing attacks when a user unknowingly hands over their password. And unfortunately, it’s almost inevitable that this will happen. This means that there will always be a question about the security of a password.
ProCircular Team
Recent Posts
Topics: Cybersecurity, Information Security, Personal Data Protection, Passwords
Let’s just say there’s a lot to learn from history without quoting Sun Tzu… again. Especially in information and cybersecurity. While much of the birth of cyber realm revolves around the military - many of the members of our community are current or former members of various armed forces - many of us still refer to the military influence of old when working through our business planning and various actions revolving around cybersecurity. A great example is the common use or reference to Boyd’s OODA (Observe–Orient–Decide–Act) loop flow chart in both attack and defensive security applications. In sticking to a military theme, I want to touch on a story from World War II and its applicability in today’s modern cybersecurity world.
Topics: Cybersecurity, Network Security, Information Security, Penetration Testing
If you’re reading this, it’s very likely that you know how to use the internet. It’s also likely you’ve made an account on the internet somewhere. When you created your last account, what kind of requirements were you forced to use? For a number of web services, these requirements still follow the 2003 NIST SP 800-63 Appendix A standards that recommend an 8-character minimum, containing one uppercase, one lowercase, one digit, and one special character (Ex: Procircular1!).
Topics: Cybersecurity, Data Protection, Personal Privacy, hacking, NIST, Passwords
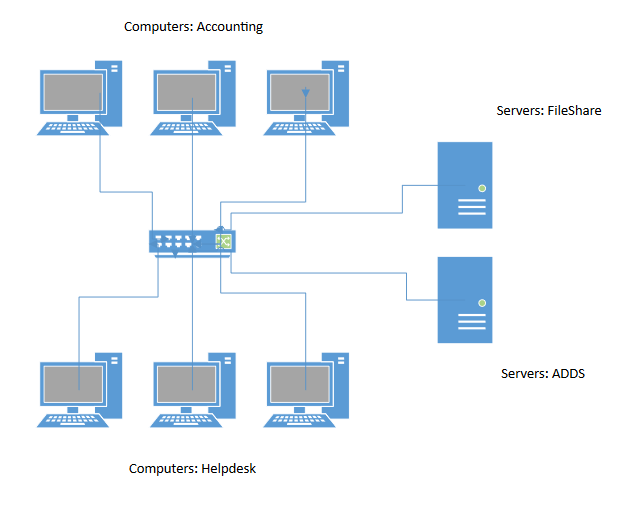
Let’s take a look at an often under-utilized aspect of network topology in the small to medium business realm: that’s right, a networking article. But before you run off, what if I told you you could increase performance and lower your production down time with equipment you (might) already have!?
Topics: Cybersecurity, Network Security, consumer security, Data Security, Data Protection, security incident handling, cybersecurity plan
During a penetration test, we’ve found that a common (and easy) way to gather credentials and gain an initial foothold on the client’s network is to perform a Man-in-the-Middle poisoning attack abusing LLMNR & NBT-NS. Depending on how active users are on the network, this attack can give an adversary valuable information almost immediately. Fortunately, with a little knowledge, this attack can be easily remediated.
What is LLMNR & NBT-NS?
Topics: Cybersecurity, Network Security, Information Security, hacking