In today’s fast-paced and remote workforce, establishing a secure remote connection is critical to conduct safe and efficient remote work. Securing this connection can be as simple as creating a jump box to access a network or device. This method allows for secure external access to internal resources without using custom firewall rules. Although there are several ways to initiate this connection, the one we’ll discuss here uses a reverse SSH tunnel through a jump box. The reverse connection process is more secure than the standard connection process, and it is the preferred option for connecting to sensitive remote devices.
The Standard Connection Process
By the traditional method of accessing a service, such as a website, the client would make a request to the webserver. The server would then return a response, in this case, a web page.
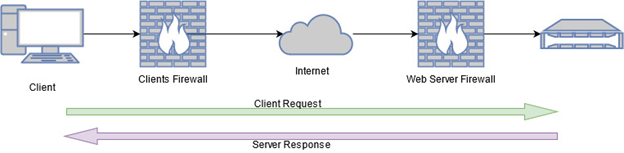
The diagram above shows the client connecting out its own firewall, through the internet, and finally through the webserver firewall to get to the webserver. The webserver firewall is required to have a rule that allows traffic to pass through to the webserver.
But what if you do not want to open any ports on your firewall? What if you want to access a sensitive service, such as a remote desktop, without exposing those services to the internet?
Remote Callbacks
This is where a remote callback can save the day! A remote callback reverses the traditional roles of a client and server. During a remote callback, the client acts as the remote device, and you become the server. The client calls out, bypassing the incoming firewall, and connects to you. This way, you have remote access, but the server’s private services are hidden behind a firewall.
Imagine a corporation has separate networks for workstations and laptops, and the firewall between them allows workstations to reach out, but laptops could not reach in.
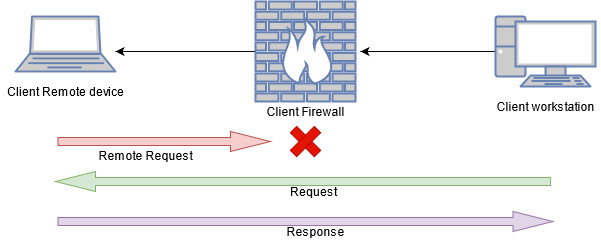
The above image shows that the remote device cannot reach in, but the workstation can reach out. This model works great in local segmented environments, but what if we need to implement this remotely over the internet? Say, for example, a Linux admin wants to manage his servers from home but does not want to open firewall ports at work or on his home network. This is where a jump box comes in.
Jump Box
A jump box is a computer that acts as a middleman for two or more connections reaching out. This is typically done using VPN or SSH connections. This middle computer allows for a secure connection from one network to another while preventing either site from creating unnecessary firewall rules or exposing services to the internet. In this example, a jump box will be hosted independently in the cloud.
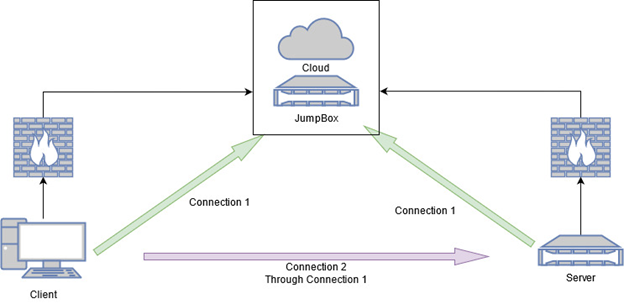
Continuing with our Linux admin and server example, the client machine and the server both connect to the jump box. Connection 1 allows the client to talk directly to the server without allowing an incoming connection on the client’s or the server’s network firewall.
Implementation
SSH is the recommended protocol as it is lightweight, secure, and supports a variety of encryption standards. Using SSH as our connection method, it will only take a few steps to turn our last example into reality.
Step 1
Ensure there is a running SSH server for both the jumpbox and server you wish to manage remotely. You’ll also need at least one user with permission to log in over SSH.
Step 2
Use a terminal and the openssh client to execute an SSH command from the server to the jump box and create a listening connection on a local interface from the jump box. This establishes Connection 1 from the server to the jump box, as shown in the diagram above.
$ ssh -N -R 4444:localhost:22 jumpboxuser@jumpbox
Let’s break down this line:
-
-
-
-
- ssh – is the command to be executed
- -N – means that you do not want to execute a command on the remote device
- -R – redirects traffic on the end device from jump box’s localhost port 4444 to our server port 22 through this ssh connection
- jumpboxuser@jumpbox – is the user and host to connect to
-
-
-
Step 3
Connect to the jumpbox from the client laptop.
$ ssh jumpboxuser@jumpbox
This establishes Connection 1 from the client to the jump box, as shown in the diagram above. When the connection is established, you should have a terminal connection on the jump box.
Step 4
Now that both devices are connected to the jump box, you may continue to connect to the server.
Connect the client device to the jump box and do the following:
$ ssh serveruser@localhost -p 4444
What is the -p flag?
p is the port number to use for this connection.
Why localhost and not the server IP?
Remember when we did the -R 4444:localhost:22? That step made a local connection available on the jump box, redirecting all traffic from jump box localhost port 4444 through the SSH tunnel to the server’s port 22.
Step 5
Done! You are now connected from the client device to the remote server without changing any firewall rules or exposing any sensitive services to the internet.
***
For more information about secure connections, visit our Contact Us page or call 844-95-SECUR.
Diagrams made with app.diagrams.net

