 The WannaCry (aka wCry or WannaCrypt) ransomware is making its way across the world, and there are several variants on their way to the united states. The original version of the ransomware behaves much like the Locky or other mainstay threats – it encrypts your data with military-grade encryption tech, starts a timer, and provides you with a place that you can pay to get a key which allows you to decrypt your valuable data.
The WannaCry (aka wCry or WannaCrypt) ransomware is making its way across the world, and there are several variants on their way to the united states. The original version of the ransomware behaves much like the Locky or other mainstay threats – it encrypts your data with military-grade encryption tech, starts a timer, and provides you with a place that you can pay to get a key which allows you to decrypt your valuable data.Unfortunately, there are a few new twists on this latest bug. While the approach isn’t unique, the delivery mechanism is derived from several cyberweapons designed by the NSA and leaked (reported) by a group called “The Shadowbrokers” within the last few weeks.
There are also additional variants of the WannaCry ransomware that may complicate things. Rather than providing a ‘real’ key they’ve been modified to simply encrypt and forget, leaving out the option of ever seeing your data again.
The research firm MalwareTech took much of the steam out of the earlier versions of this ransomware. Without going into technical detail, the firm registered the domain of the site that the application uses to ‘call home’ and essentially stops it from propagating. Unfortunately, though, the new variants either use a new site or remove the ‘call home’ completely.
The most important things that organizations can do to protect yourself are listed below and adapted from some recent work by Troy Hunt at Microsoft. I’ve taken the liberty of changing the order of the recommendations so that if you only do one thing it’s at the top:
- BACKUP. You must have your data backed up to an external drive that is not always connected to your machine. Better still use two or more drives and rotate them offsite. Cloud storage is good, but it is usually synchronized and so still at risk from ransomware, see Backups and Cloud Storage. MANAGEMENT: Ask IT when the ran a full backup, and then when they’ve performed their most recent restore of those data. If the answer isn’t ‘last weekend’ you’ll want to insist that they do both today or tonight.
- Update your Operating Systems. Make sure you stay on a supported version of Windows, or even better on the latest version of Windows which is the most secure. In short, stop using Windows XP and get all your machines upgraded to Windows 10. For companies complaining about the costs of upgrades, what are the costs of losing all your data? MANAGEMENT: Ask IT about your patch management policy, and ask that they ‘push a patch’ to all of the workstations possible this morning.
- Make sure that Windows Update is running and keep your machines updated with the latest security patches and driver fixes.
- Have an anti-virus installed and keep it up to date. I just use Windows Defender that comes with Windows. We also recommend MalwareBytes, and for corporate security we’ve seen excellent results with Carbon Black. Sadly, anti-virus programs often cannot protect from these sorts of attacks. Our colleagues at Watchpoint also have an excellent solution to ransomware challenges. MANAGEMENT: If you haven’t done an IT Risk Assessment that includes patch management, now would be an excellent time to do so.
- Don’t Click That. Don’t open suspicious emails or open attachments. Most successful attacks and hacks in recent years have not been from viruses or trojans. They have been because users were tricked by phishing and social engineering scams into giving their credentials away on fake websites or executing malicious software. MANAGEMENT: Phishing and social engineering are the easiest methods that hackers can use against your company. Protect yourself with Employee Awareness Training and bring them to you defense.
To pay or not to pay? Our advice is usually determined on a case by case basis. In the past we'd generally have recommended paying, but many of our sources lead us to believe that your likelihood of getting keys is lower with this particular strain.
ProCircular is available to assist with any sort of cybersecurity challenge. We can help to walk you through the steps necessary to deal with WannaCry or any other bug, and once you’re out of the woods we help you to avoid danger in the future.
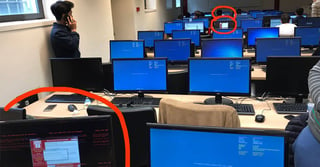
(Image source: The Hacker News)


